Symantec Endpoint Protection 15 Crack + Pre-Activated 2026
Symantec Endpoint Protection Crack With Full Version Free Download
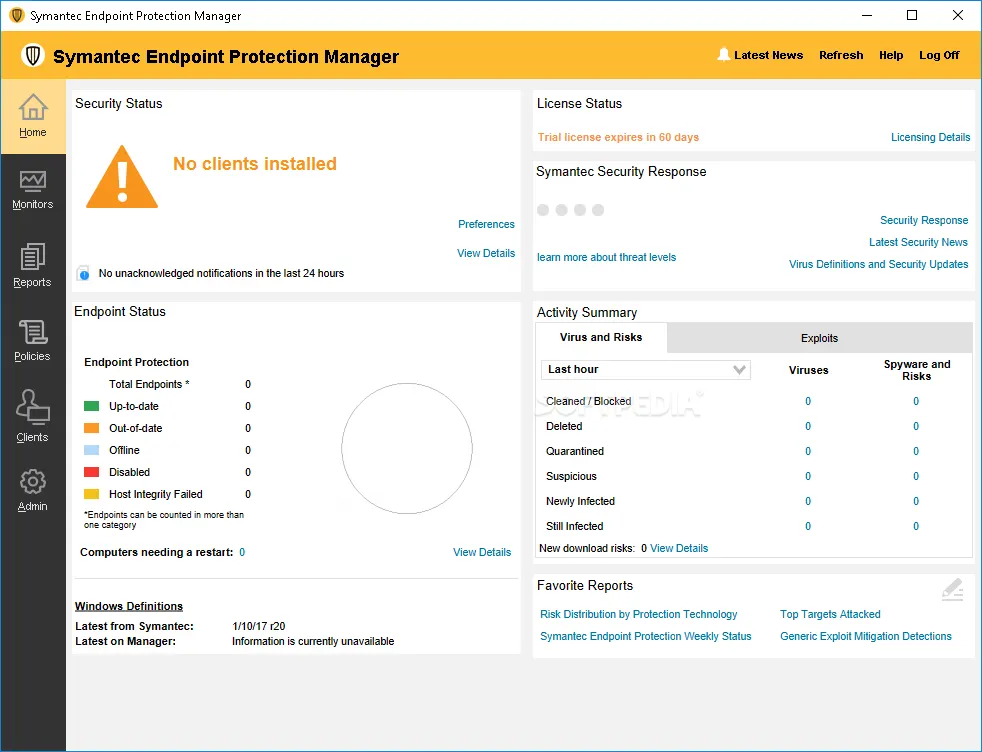
Symantec Endpoint Protection Crack is a professional, cloud-based endpoint security solution that is of high quality and is designed to safeguard servers and desktops in small enterprises. Maximize protection and optimize security by securing all endpoints with a single agent that utilizes advanced machine learning and behavioral analysis to fine-tune detection engines. It is compatible with the majority of desktops, including Windows, Mac, Linux, and virtual environments. Antivirus, firewall, and intrusion prevention, application and device control, host integrity, and system lockdown comprise its fundamental capabilities.

You May also download: Aiseesoft Screen Recorder
Symantec Endpoint Full Version provides multiple levels of security to defend endpoints, such as a user’s computer and network, from threats. Symantec Endpoint Protection Download is computer and electronic device needs it, but regular use degrades its performance. It’s a one-stop shop for security against any and all forms of cybercrime. Both the effectiveness and security of the system are guaranteed. There are a number of special options for the user to play with.
People Can also like: Outbyte Pc Repair
Symantec Endpoint Protection Crack + Latest Version Free Download
Most computer users will not require extensive training to begin using Latest Symantec Endpoint Protection Version, and its free download is likely to have contributed to its widespread appeal. You’ll have everything at your disposal to prevent being caught off guard by cyberattacks. In this way, you can rest assured that your crew can focus on their task without distraction. While most people have simply learnt to accept it, we’re taking decisive action.
Symantec Endpoint Protection is massive disobedience at a workplace is a torrent of lies, resistance, awareness, and countermeasures. Symantec Endpoint Protection Crack is at the top of Gartner’s list for premise alarm systems due to its strength in both implementation and vision. The company’s access control product is available in a number of feature-rich variants and promotes creativity and independence.
Key Features Of Symantec Endpoint Protection Free Download:
- Multi-layered security, including signatureless and centralized endpoint solutions, is necessary to combat widespread ransomware and other unanticipated threats.
- Superior defense compared to standard virus scanners
- To make speedy adjustments to the automatically enforced system access handle, you don’t have to release new software.
- If a Trojan causes your computer to freeze, you will lose access to all open programs until the issue is fixed.
control over one’s physical space and access to helpful applications. - Security administration that monitors both physical and digital gadgets from a single dashboard.
- Symantec Endpoint Security earlier version manuals are easy to follow.
- A comprehensive virus database is integrated for complete computer safety.
- Consistency with the native Windows storage and retrieval features.
- Symantec Endpoint Protection Crack acts as a firewall to prevent harmful malware from accessing servers, making them reliable at all times.
- The program improves both the actual and virtual safety of computer systems.
What’s New In Symantec Endpoint Protection:
- Users are routed from problematic sites to Vertical strain via a Mac document, where they may manage their connections and bandwidth usage with the aid of individualized logs.
- Improved defenses against attacks are now feasible because to technological developments in areas such as pattern recognition and behavioral monitoring, as well as in critically important ancillary capabilities like
- firewalls and vulnerability screening.
- The cyber defenses of the future will be powered by the United States’ most comprehensive private risk surveillance program.
Symantec Endpoint Protection System Requirements:
- Pentium III or later 32-bit Intel CPU (Pentium 4 or later is recommended) need minimum GHz
- A 64-bit Pentium 4 with at least 2 GHz of CPU speed is necessary. x86-64 compatibility is preferred.
- One gigabyte of random-access memory is available.
How To Install Symantec Endpoint Protection Crack?
- Before beginning the process of installing the application, it is essential to ensure that the download was completed successfully, without interruptions, and in its entirety.
- Before continuing with the installation procedure, this step of verification must be completed.
- Before moving on to the next method step, we must ensure that this one has been completed successfully.
- At this point, there should be no remaining obstacles that must be surmounted in order to complete the procedure.
- The only remaining task is to ensure that everything goes as planned.
- Verify that this is indeed the case is the only remaining task at this juncture.
Technical Information:
- File type : Compressed / Zip & RAR (Use 7zip or WINRAR to un zip File)
- Support OS : All Windows (32-64Bit)
- Virus Status : 100% Safe Scanned By Antivirus




THANKS, ADMIN FOR THIS GREAT POST. I LOVE YOUR CONTENT