Havij Pro v1.18 Crack + Portable Free Download 2025
Havij Pro Crack + Full Version Free Download 2025
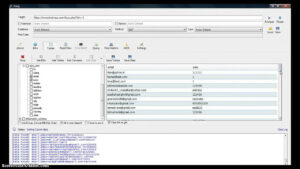
Havij Pro Crack is a fully automated injection attack software that helps security flaw researchers locate and exploit website vulnerabilities. This can be facilitated by narrowband technology. Using a spine network fingerprint, the same user could use this software to obtain Database identities and encrypted passwords. Additionally, users can extract data, unload data structures, and execute Relational operations.
You Can Also Like the Havij Download

Havij Pro features a graphical user interface (GUI) similar to that of a smartphone, making it easy for human administrators to access necessary data. The simplicity of Havij Pro for Windows 11 has the potential to empower non-technical users, allowing them to conduct tasks without relying on software attackers. This tool enables methods that store root permissions and also allows for command execution within the Linux kernel.
Havij Pro Crack + Latest Version Free Download
The Havij Pro Mac desktop application enables users to authenticate against various networks. One of the services it offers is a keyword search for relevant data. At this time, accounts stored in the database can be retrieved. Additionally, a straightforward marketing manual is included with the application. It features a function that allows users to save information to a file. To get started, you can download Havij Pro and purchase accessible solutions for knowledge restoration to address the website’s many vulnerabilities.
Havij Pro employs an automated tool that detects and exploits SQL Injection vulnerabilities in websites, which can be compromised by a vulnerable web application. The cracked version of Havij Pro provides access to the file system and shell commands, database login names and hashes, as well as dumps of tables and columns. Users can also execute SQL queries directly on the server.
You Can Also Like: EEZCheck Printing Software
Key Features Of havij 1.18 pro full crack:
- The capacity to correct faults
- Complete support for HTTPS
- There are numerous updates available.
- The instrument includes an XML format for data storage.
- The log can be downloaded.
- David Mac assesses critical phrases.
- The document is accessible to users.
- Added blind testing for MS SQL.
- Microsoft Access testing was introduced, exclusively for the business model.
- Testing for MySQL was enabled.
- There is a consumer guide available.
- The information-dumping files are now available. Havij Free Download For Windows 7 64 Bit contains an error-
- Havij Pro Download correcting feature.
- MySQL lacks
- Databases supported include:
- MySQL temporal
- Union-based MySQL with error-based MySQL Group Following Oracle
What’s New in Download Havij 1.18 Pro Cracked?
- A method for correcting inaccuracies
- Comprehensive assistance with Sal’s certificate
- There are numerous indispensable elements of knowledge.
- The instrumentation includes a variety of data storage formats that can be used to save the collected information.
- The client can delete the record throughout this scenario.
- Havij Macintosh strongly suggests using keyword density filtering.
System Requirements:
- Windows XP, Vista, Windows 7, Windows 8, Windows 8.1, and Windows 10
- The memory is 512 megabytes in size.
- Disk Space: 25 MB. A dual-core.
- Dual-core Intel processor as the CPU.
How To Install Havij Pro Crack?
- First and foremost, retrieve Havij from his current position.
- Save Havij to your bookmarks first, then add a bookmark to any other website or file on your computer.
- You must, therefore, select a website that appears to be vulnerable to cross-site scripting to exploit it.
- You are highly interested in launching Havj and have observed its positioning.
- Lastly, when launching Havij, visitors are required to input the address of the legitimate website.
- Next, select the “Analyze” option, which will investigate the area in question and determine whether session hijacking is possible.
- Havij will identify the computer and the software running on it, and as a result, a notification will be displayed.
Technical Information:
- File type: Compressed / Zip & RAR (Use 7zip or WINRAR to unzip the file)
- Support OS: All Windows (32-bit and 64-bit)
- Virus Status: 100% Safe Scanned By Antivirus

Recent Comments